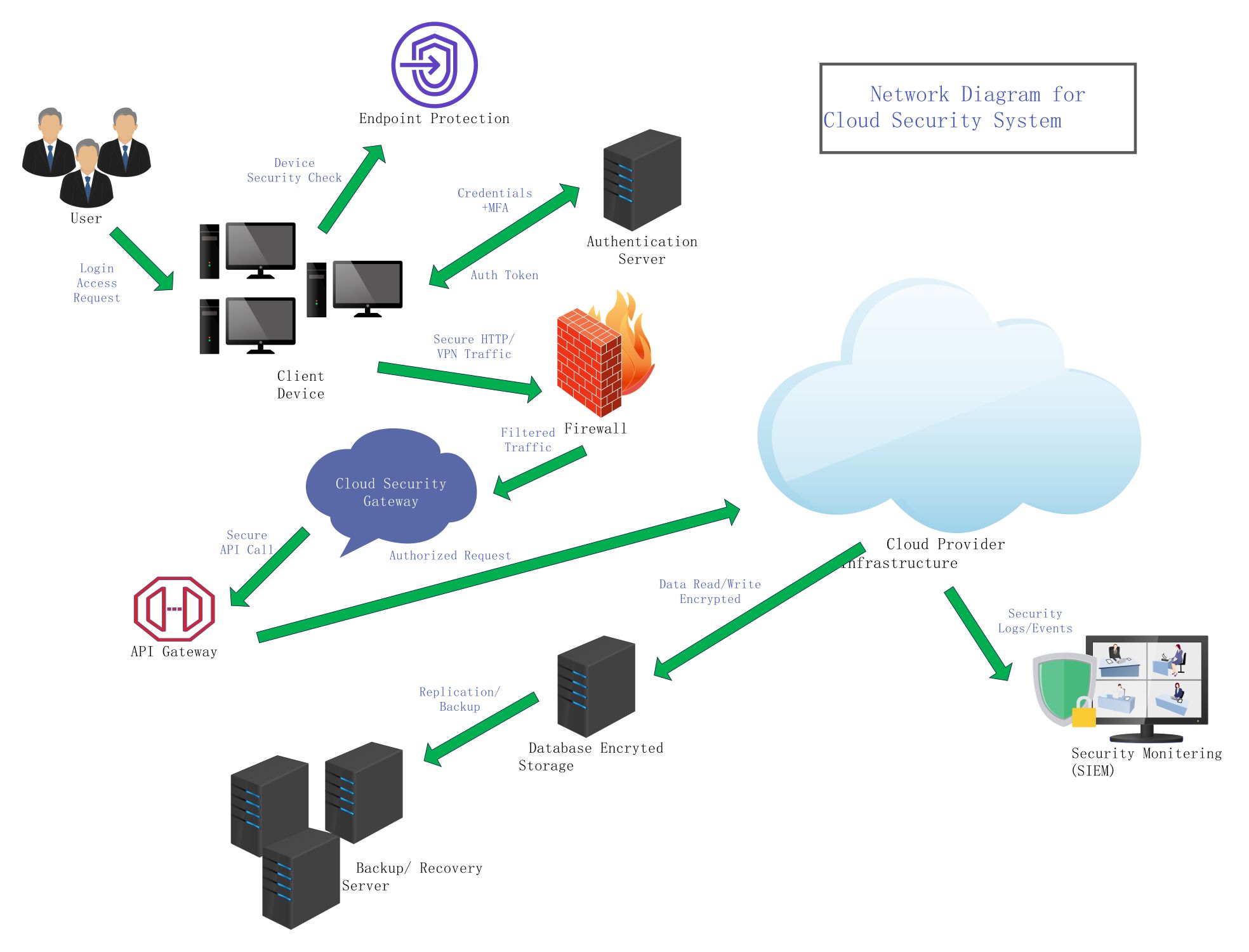
About this Network Diagram for Cloud Security template
This template provides a visual guide for building a safe cloud environment. It covers user access, data storage, and monitoring. You can use it to plan your infrastructure and ensure all security layers are active and properly integrated across your network.
Identity and Access Control
This section manages how users enter the system safely. It uses multi-factor authentication and token-based logins to verify identities. This prevents unauthorized people from reaching sensitive data or changing settings within the cloud network.
- User Login Requests
- Multi-Factor Authentication (MFA)
- Authentication Server
- Secure Auth Tokens
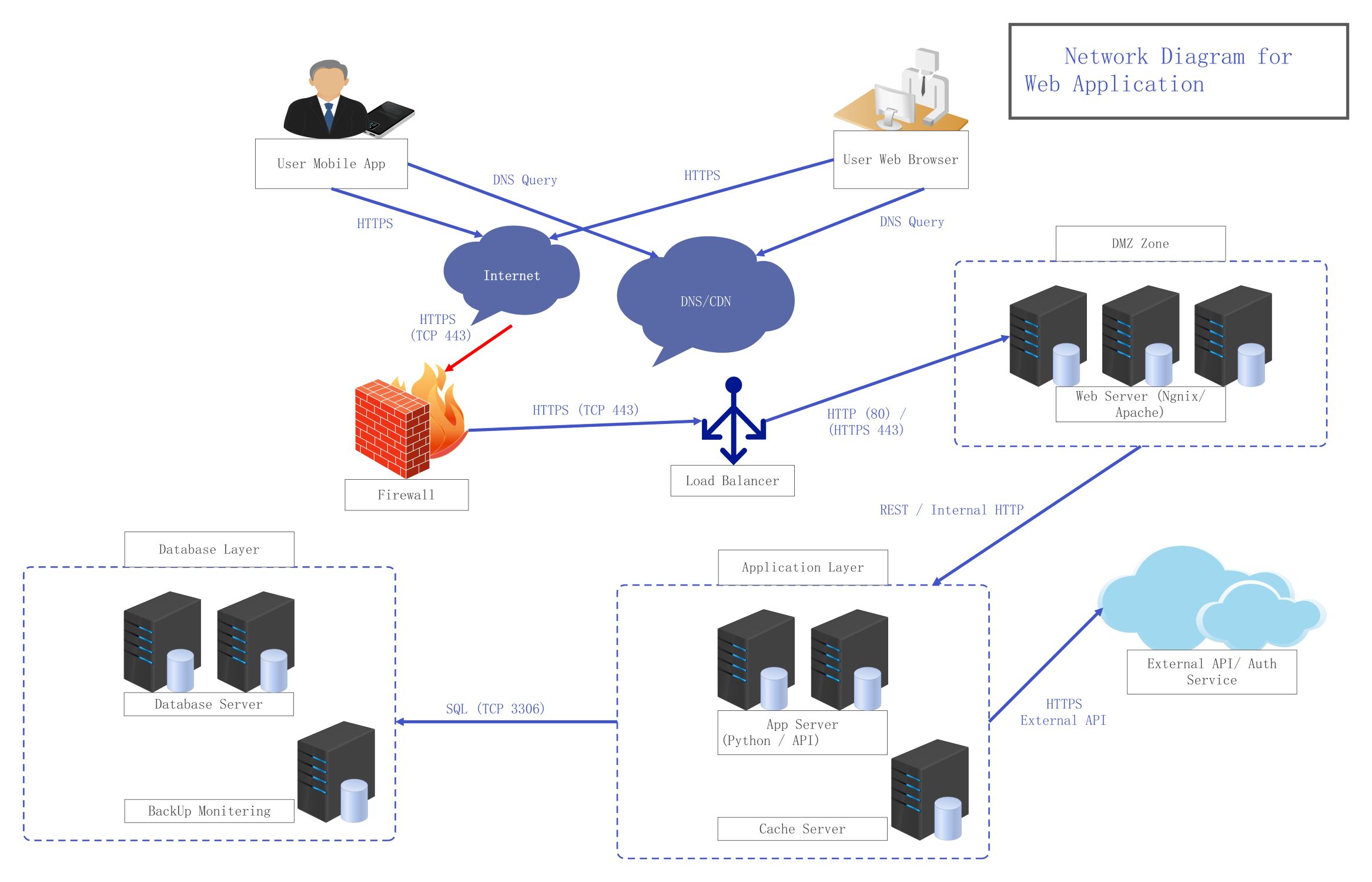
Network Perimeter Defense
Network defense focuses on filtering traffic before it reaches the cloud. It uses firewalls and secure gateways to block harmful data. This ensures that only safe, encrypted traffic moves between the client devices and the cloud provider.
- Firewall Filtering
- Cloud Security Gateway
- Secure HTTP/VPN Traffic
- API Gateway Integration
Data Storage and Recovery
Data security involves protecting information while it sits in storage. It uses encryption to keep files private. The system also includes automated backups and recovery servers. This ensures data stays safe and available even if an error occurs.
- Encrypted Database Storage
- Replication and Backup
- Backup/Recovery Server
- Data Read/Write Encryption
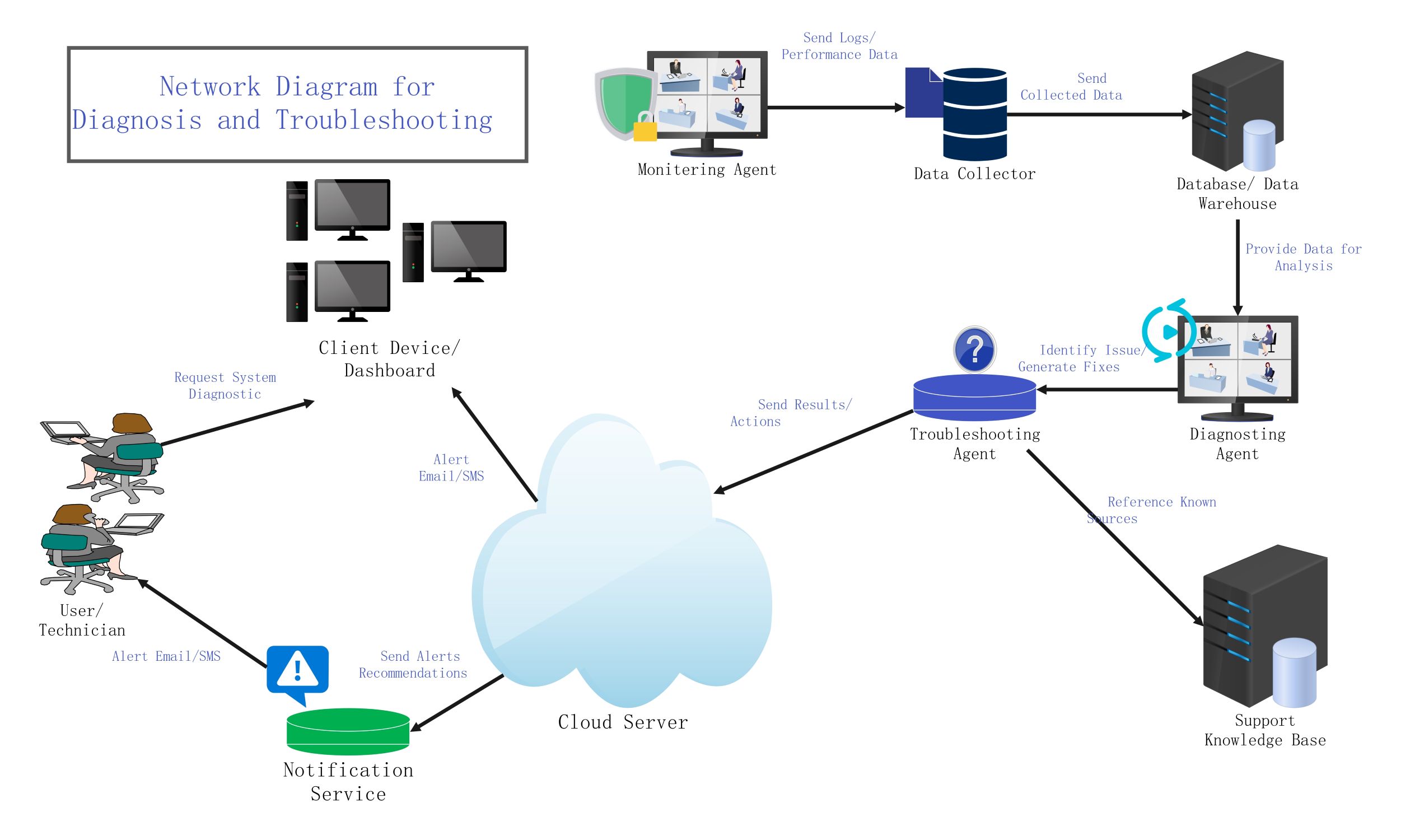
Security Monitoring and Infrastructure
Monitoring keeps track of all activities within the cloud system. It uses SIEM tools to watch for unusual events or security logs. This continuous oversight helps teams find and fix potential threats quickly before they cause damage.
- Cloud Provider Infrastructure
- Security Monitoring (SIEM)
- Security Logs and Events
- Infrastructure Oversight
FAQs about this Template
-
Why is a cloud security diagram important for businesses?
A cloud security diagram acts as a blueprint for your digital safety measures. It allows IT teams to visualize where data flows and where security gaps might exist. By mapping out firewalls, gateways, and encryption points, businesses can ensure they meet compliance standards. It also serves as a critical reference tool during security audits or incident response procedures.
-
What is the role of an API Gateway in this diagram?
An API Gateway acts as a secure entry point for all application programming interface requests. It manages traffic by authenticating users and validating data before it reaches the backend services. This prevents malicious attacks like SQL injection or denial-of-service attempts. By centralizing these security checks, the gateway ensures that every interaction with your cloud infrastructure remains strictly controlled and monitored.
-
How does SIEM improve cloud safety within the network?
SIEM stands for Security Information and Event Management. It collects and analyzes log data from various sources across your network in real-time. This helps security teams detect suspicious patterns that might indicate a cyberattack. By providing a single view of the entire environment, SIEM allows for faster response times to threats, helping to minimize potential data loss or downtime.