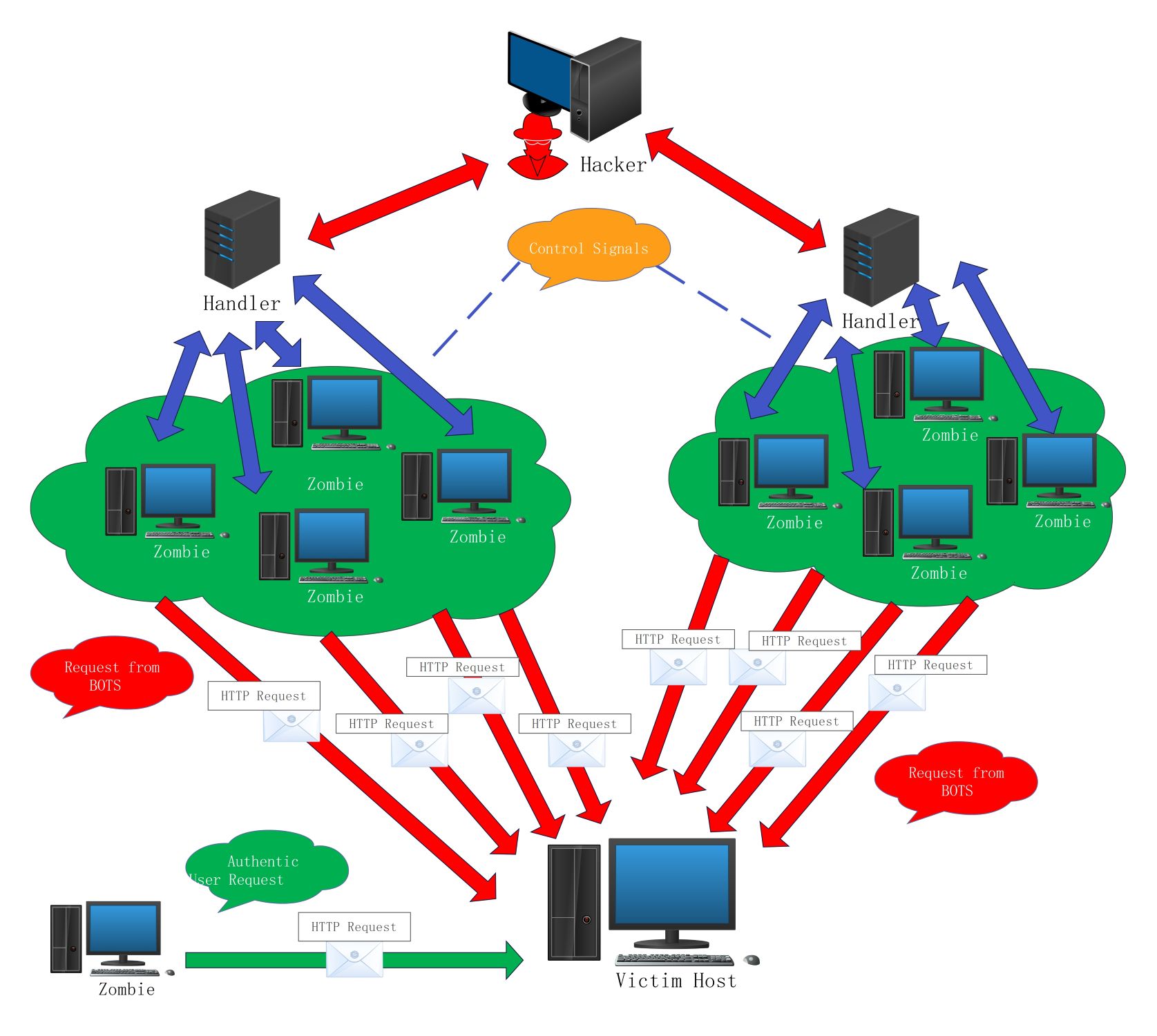
About this Network diagram for DDoS template
This network diagram illustrates the complex layers of a Distributed Denial of Service attack. It visualizes how an attacker coordinates multiple compromised systems to target a single host, making it easier for IT professionals to explain security risks.
Central Hacker Control
The hacker acts as the mastermind behind the entire DDoS operation. They send specific control signals to intermediate servers to maintain anonymity and coordinate the timing of the massive traffic flood against the victim.
- Hacker Command Station
- Control Signals
- Attack Initiation
Intermediate Handlers
Handlers serve as the command-and-control layer between the hacker and the botnet. They distribute instructions to thousands of infected machines, ensuring the attack is synchronized while keeping the hacker's direct identity hidden from security logs.
- Server Handlers
- Instruction Distribution
- Communication Relay
Botnet Zombies
Zombies are compromised computers or IoT devices that make up the botnet. These machines appear to be normal systems but are actually following orders to send high volumes of HTTP requests to the target simultaneously.
- Compromised Zombie Computers
- Automated Botnets
- HTTP Request Generation
Victim Host Target
The victim host is the final destination of the coordinated attack. It receives a overwhelming mixture of legitimate traffic and malicious bot requests. This flood consumes system resources, eventually causing the service to crash or become unavailable.
- Victim Server
- Service Disruption
- Resource Exhaustion
FAQs about this Template
-
How does a DDoS network diagram help in cybersecurity training?
A DDoS network diagram provides a visual representation of how attackers structure their infrastructure. By seeing the layers between the hacker and the victim, security teams can identify potential points for mitigation. It helps students and staff understand that attacks are not just single connections but complex networks involving handlers and compromised bots that require multi-layered defense strategies.
-
What is the role of a handler in a DDoS attack?
Handlers act as a middle layer that helps hackers manage large botnets without exposing their own IP addresses. They receive commands from the attacker and relay them to hundreds or thousands of zombie machines. This hierarchical structure makes it harder for law enforcement to trace the attack back to the source and allows for more efficient synchronization of traffic.
-
Why is it difficult to stop the requests from zombies?
Stopping zombie requests is difficult because they often look like legitimate user traffic. Since the requests come from thousands of different IP addresses globally, simply blocking one source does not stop the attack. Security systems must use advanced behavior analysis and rate limiting to distinguish between a real customer and a bot trying to overwhelm the server resources.